Okay, so check this out—DeFi used to mean hopping between a handful of EVM chains and praying your MetaMask didn’t freeze on a gas spike. Wow. Things have changed fast. Now users expect seamless movement across 10, 20, sometimes dozens of chains. That shift isn’t just convenience; it’s reshaping security trade-offs, gas strategies, and how you think about custody.
At first glance multi‑chain wallets look like a UX win: one seed, one interface, many chains. My instinct said “this solves everything.” But actually, wait—there are layered risks that arrive with that simplicity. One key reality: the wallet surface area grows with every chain you add. More chains, more RPC endpoints, more signing contexts, more places where a bug or a misconfiguration can leak value. On one hand you get unified asset visibility; on the other, your attack surface expands. Hmm… that’s the core tension.
So let’s walk through the practical parts—what a multi‑chain wallet should give you, how to optimize gas across chains without getting nickeled to death, and the must‑do security hygiene that every DeFi user needs. I’ll be honest: I’m biased toward wallets that prioritize actionable UX and clear transaction metadata, because slapping a raw hex on a user and asking them to sign is a terrible user experience and a security hazard.

What a robust multi‑chain wallet actually needs
First, fast checklist: network management, clear chain context in every signing prompt, and sane defaults for gas estimates. Seriously—if the wallet doesn’t tell you which chain a signature will be broadcast to, don’t trust it. Also, local transaction history and optional offline signing help a lot when you want to audit what you’ve done.
Second, sane RPC handling. Many wallets rely on public RPCs for convenience. That can be okay, but public endpoints are throttled, unreliable, and sometimes return inconsistent states. A good wallet should allow curated, trustworthy RPCs and let advanced users plug in their own. Initially I thought “any RPC is fine,” but then a reorg on a congested chain taught me that incorrect nonce handling can result in stuck transactions and duplicated spends—ugh.
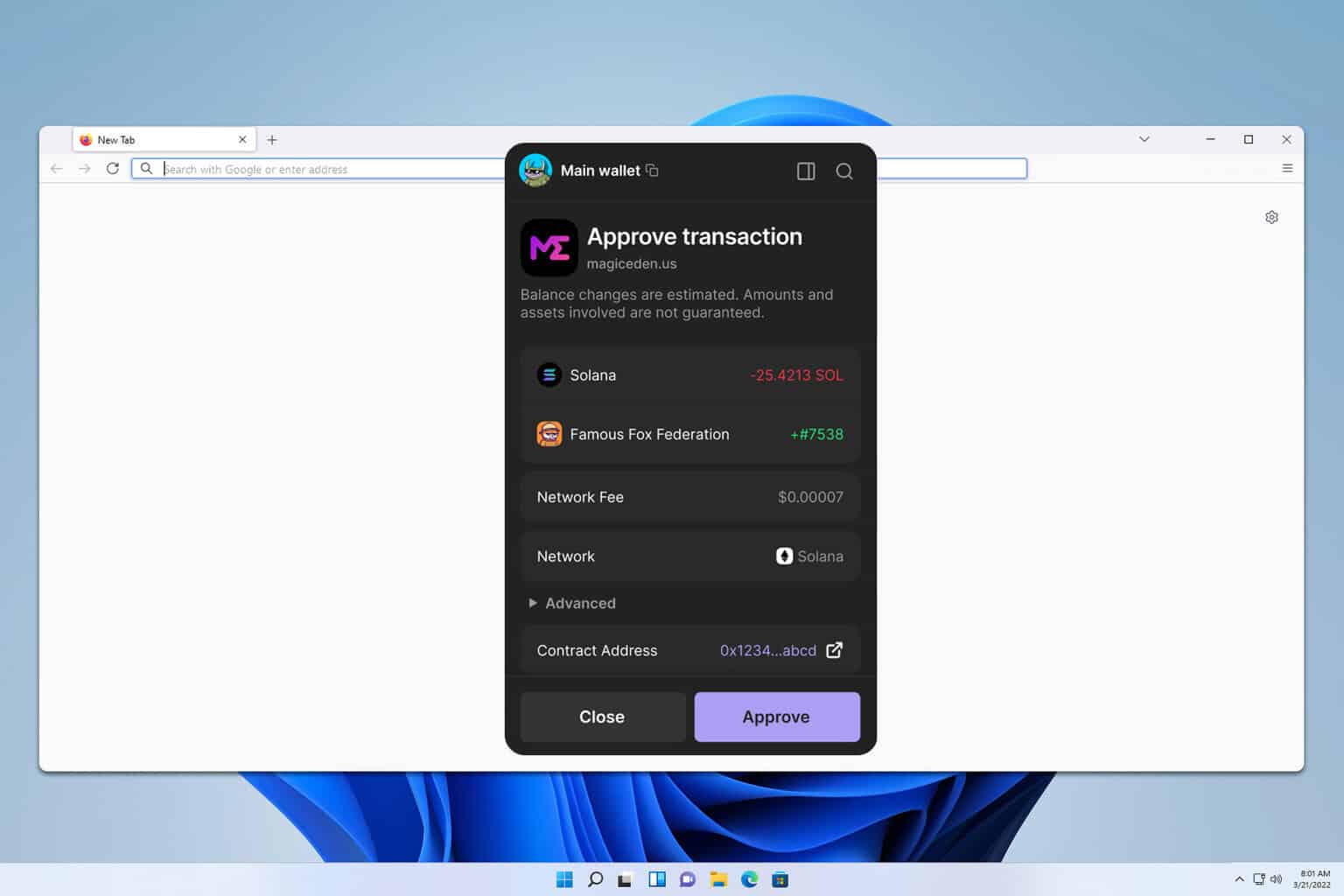
Finally, interoperable token metadata and cross‑chain approval management. That means the wallet surfaces approvals, lets you revoke them, and warns when a dApp requests broad allowances. Too many wallets hide approve details behind pages of gobbledygook, which is a big problem.
Gas optimization strategies that actually help
Gas is a UX tax. On L1s it can bankrupt a trade; on rollups it eats margin. Here are approaches that move the needle.
Batched transactions and bundle relays. If you’re doing multiple related actions (approve, deposit, swap), bundling them server‑side or using a relayer can reduce duplicative gas. There are tradeoffs—trusted relayers introduce counterparty risk—so weigh that carefully.
Use meta‑transactions where supported. Meta‑txs let a relayer submit on behalf of the user, which can push gas costs to a dApp or aggregator. Not all chains or contracts support it, but when implemented well it smooths gas exposure.
Optimistic routing and destination fee awareness. Some multi‑chain tools will suggest moving value through a cheaper intermediate chain to save on aggregate fees, though that adds complexity and time. On one hand you save gas; on the other, you’re exposing funds to an extra bridge step, which itself is a risk.
DeFi security: habits that save money and nerves
Here’s what bugs me about common advice: it’s often too abstract. “Use hardware wallets.” Fine—how? Where? Let me be specific.
1) Separate accounts by risk. Keep a hot wallet for small, active trades and a cold wallet for holdings you want long‑term. Move only the amount you need. This isn’t sexy, but it’s very effective.
2) Use approvals sparingly. Approve only the precise amount or use one‑time approvals when possible. Check and revoke allowances regularly. Some wallets show a permission dashboard—use it.
3) Turn on transaction details and domain verification. Good wallets display the contract address, the human readable domain (via EIP‑1271 or similar), and the calldata breakdown. If you can’t interpret calldata, pause and verify on block explorers or developer docs. My gut told me “that transaction looks off” more than once—it was worth listening to.
4) Multi‑sig for shared funds. If you’re managing communal or treasury assets, require multiple keys. It adds friction, yes, but it dramatically reduces single‑point failures.
Choosing a multi‑chain wallet: UX, security, and the middle ground
Not all wallets aim for the same tradeoffs. Some prioritize automation; others push control. Personally, I prefer wallets that strike a balance—clear prompts, strong defaults, and advanced options tucked away for power users. One wallet I’ve used that nails this blend is rabby wallet, which surfaces approvals, gives clear chain context, and supports multi‑chain flows without feeling like a Swiss Army knife shoved into your face. That said, every user has different threat models—your needs may differ.
Think about these questions when picking a wallet: Are approvals visible and revocable? Can you plug in your own RPC or hardware signer? Does the UX reduce accidental approvals and clearly show chain context? Answer those and you’ll be ahead of most users.
Common failure modes (and how to avoid them)
Bridge rollover mistakes. Moving funds across chains via bridges is routine, but bridging adds a dependency: the bridge contract. Audit the bridge, test with small amounts, and watch for slippage or routing quirks.
Replay and nonce confusion. When using multiple networks or relayers, nonce management can get messy. Prefer wallets that transparently manage nonces or allow manual nonce controls for advanced users.
Phishing and fake dApps. Always double‑check domain names and contract addresses. Copying a URL from search results or social media can land you on a malicious dApp. Bookmark your frequently used sites.
FAQ
Can one wallet truly be secure across dozens of chains?
Yes, but only if the wallet enforces clear chain context, supports secure RPCs, and provides strong signing UX. Security is about good defaults plus user habits—no single feature is a panacea.
How do I save gas without compromising security?
Use batching or meta‑txs when available, choose cheaper routing paths cautiously, and avoid constantly executing on congested L1s. But never offload security—relayers and aggregators introduce trust assumptions you should understand.
Should I use an account abstraction or stick with EOA + hardware wallet?
Account abstraction (smart accounts) brings great UX: session keys, gas payment flexibility, and better recovery flows. However, they require careful design and audited infrastructure. For large, long‑term holdings, a hardware multisig is still a gold standard.
Alright—so what’s the bottom line? Multi‑chain wallets are powerful because they reduce friction, but that same simplicity can hide complexity. Be deliberate: segment funds, review approvals, and understand any relayer or bridge you use. Keep your UX expectations realistic—no wallet will make you invincible—but the right one will keep you comfortably in control while you navigate a collection of chains that keeps getting bigger. I’m not 100% sure where the next big attack vector will appear, but improving the small habits above will prevent the most common losses.